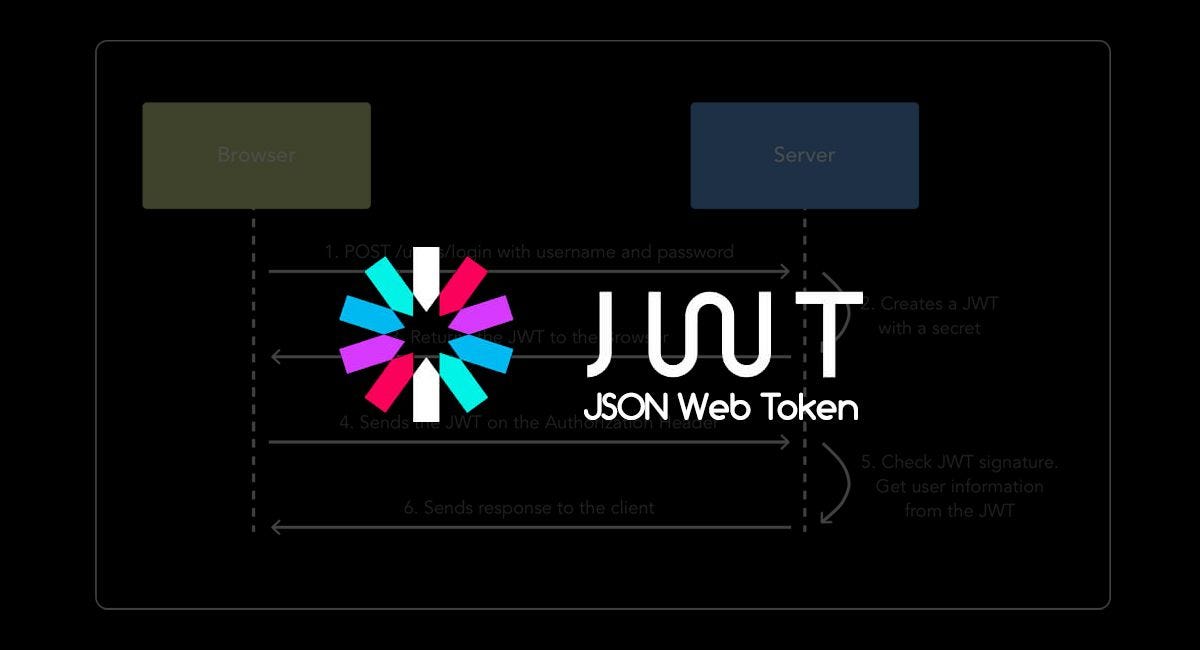
JSON Web Token (JWT) — The right way of implementing, with Node.js | by Siddhartha Chowdhury | Medium
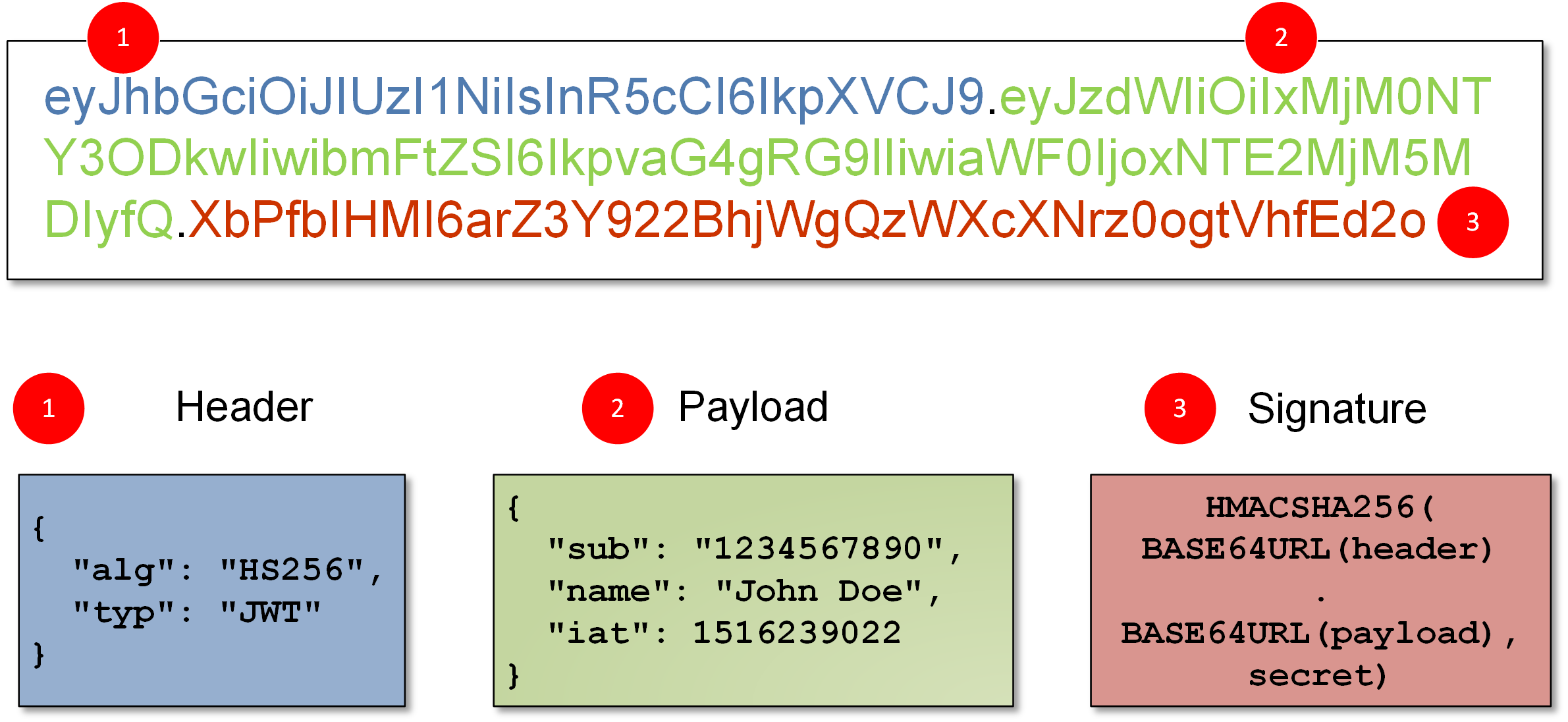
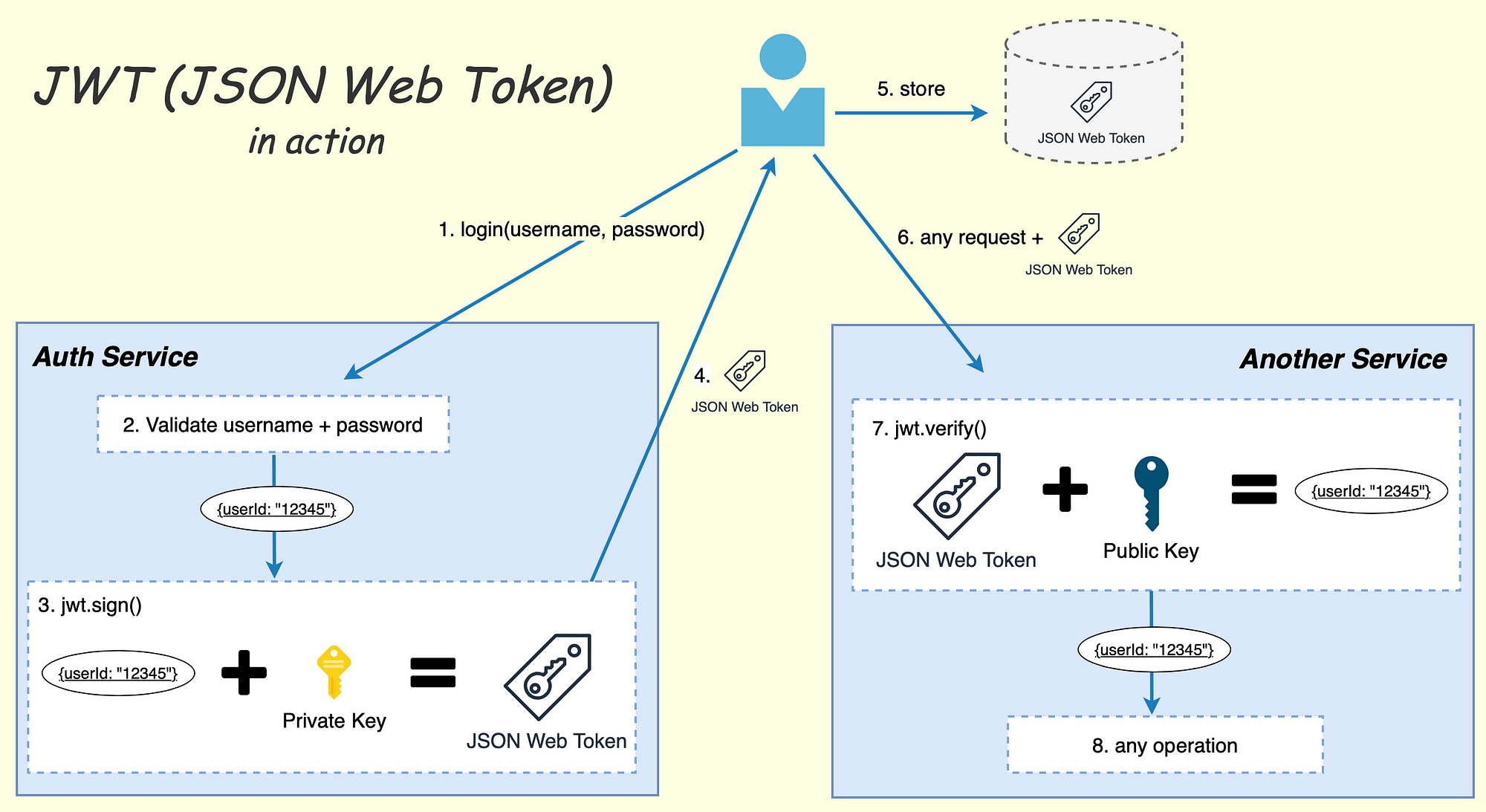
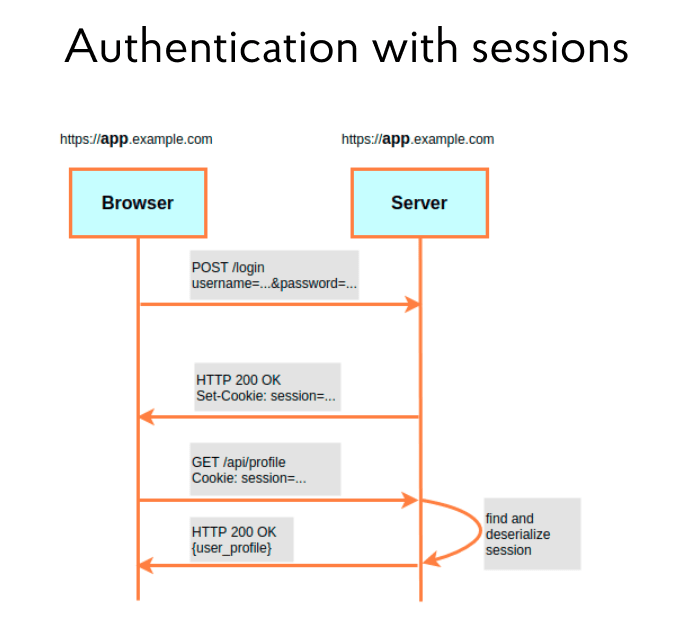
Understanding JSON Web Tokens (JWT): A Secure Approach to Web Authentication | by Extio Technology | Medium

Understanding JSON Web Tokens (JWT): A Secure Approach to Web Authentication | by Extio Technology | Medium

Ultimate Guide to Securing Your Application with JWT: Best Practices and Tips | by Obi kastanya | Medium

.jpg)